.configuration options using the ssh, scp, and sftp -o option. Ssh/config should be used if specific configuration is required for jump hosts. High Speed Premium VPN and Fast SSH ServerSSH dropbear - High Speed Premium VPN and Fast SSH Server, High Data Transfer High Speed Connection SSH account, ssh account 30 days, ssh server, free ssh.
-->To automate tasks that create and manage files on a Secure File Transfer Protocol (SFTP) server using the Secure Shell (SSH) protocol, you can create automated integration workflows by using Azure Logic Apps and the SFTP-SSH connector. SFTP is a network protocol that provides file access, file transfer, and file management over any reliable data stream.
Download Termius – SSH/SFTP and Telnet client APK for android The description of Termius – SSH/SFTP and Telnet client Termius is the best way to manage, UNIX and Linux systems, whether that would. HTML versions of the OS X, OS X Server, Xcode Tools, and CHUD man pages. I'm try to configure proftpd for use with SFTP and use with virtual users, but after try several ways it not works with virtual users. Only works for system usersSome config relative to problem b.
Here are some example tasks you can automate:
Sftp Ssh_config
- Monitor when files are added or changed.
- Get, create, copy, rename, update, list, and delete files.
- Create folders.
- Get file content and metadata.
- Extract archives to folders.
In your workflow, you can use a trigger that monitors events on your SFTP server and makes output available to other actions. You can then use actions to perform various tasks on your SFTP server. You can also include other actions that use the output from SFTP-SSH actions. For example, if you regularly retrieve files from your SFTP server, you can send email alerts about those files and their content using the Office 365 Outlook connector or Outlook.com connector. If you're new to logic apps, review What is Azure Logic Apps?
For differences between the SFTP-SSH connector and the SFTP connector, review the Compare SFTP-SSH versus SFTP section later in this topic.
Limits
The SFTP-SSH connector currently doesn't support these SFTP servers:
- IBM DataPower
- MessageWay
- OpenText Secure MFT
- OpenText GXS
SFTP-SSH actions that support chunking can handle files up to 1 GB, while SFTP-SSH actions that don't support chunking can handle files up to 50 MB. The default chunk size is 15 MB. However, this size can dynamically change, starting from 5 MB and gradually increasing to the 50-MB maximum. Dynamic sizing is based on factors such as network latency, server response time, and so on.
Note
For logic apps in an integration service environment (ISE),this connector's ISE-labeled version requires chunking to use the ISE message limits instead.
You can override this adaptive behavior when you specify a constant chunk size to use instead. This size can range from 5 MB to 50 MB. For example, suppose you have a 45-MB file and a network that can that support that file size without latency. Adaptive chunking results in several calls, rather that one call. To reduce the number of calls, you can try setting a 50-MB chunk size. In different scenario, if your logic app is timing out, for example, when using 15-MB chunks, you can try reducing the size to 5 MB.
Chunk size is associated with a connection. This attribute means you can use the same connection for both actions that support chunking and actions that don't support chunking. In this case, the chunk size for actions that don't support chunking ranges from 5 MB to 50 MB. This table shows which SFTP-SSH actions support chunking:
Action Chunking support Override chunk size support Copy file No Not applicable Create file Yes Yes Create folder Not applicable Not applicable Delete file Not applicable Not applicable Extract archive to folder Not applicable Not applicable Get file content Yes Yes Get file content using path Yes Yes Get file metadata Not applicable Not applicable Get file metadata using path Not applicable Not applicable List files in folder Not applicable Not applicable Rename file Not applicable Not applicable Update file No Not applicable SFTP-SSH triggers don't support message chunking. When requesting file content, triggers select only files that are 15 MB or smaller. To get files larger than 15 MB, follow this pattern instead:
Use an SFTP-SSH trigger that returns only file properties. These triggers have names that include the description, (properties only).
Follow the trigger with the SFTP-SSH Get file content action. This action reads the complete file and implicitly uses message chunking.
Compare SFTP-SSH versus SFTP
The following list describes key SFTP-SSH capabilities that differ from the SFTP connector:
Uses the SSH.NET library, which is an open-source Secure Shell (SSH) library that supports .NET.
Provides the Create folder action, which creates a folder at the specified path on the SFTP server.
Provides the Rename file action, which renames a file on the SFTP server.
Caches the connection to SFTP server for up to 1 hour. This capability improves performance and reduces how often the connector tries connecting to the server. To set the duration for this caching behavior, edit the ClientAliveInterval property in the SSH configuration on your SFTP server.
Prerequisites
An Azure subscription. If you don't have an Azure subscription, sign up for a free Azure account.
Your SFTP server address and account credentials, so your workflow can access your SFTP account. You also need access to an SSH private key and the SSH private key password. To upload large files using chunking, you need both read and write access for the root folder on your SFTP server. Otherwise, you get a '401 Unauthorized' error.
The SFTP-SSH connector supports both private key authentication and password authentication. However, the SFTP-SSH connector supports only these private key formats, algorithms, and fingerprints:
- Private key formats: RSA (Rivest Shamir Adleman) and DSA (Digital Signature Algorithm) keys in both OpenSSH and ssh.com formats. If your private key is in PuTTY (.ppk) file format, first convert the key to the OpenSSH (.pem) file format.
- Encryption algorithms: DES-EDE3-CBC, DES-EDE3-CFB, DES-CBC, AES-128-CBC, AES-192-CBC, and AES-256-CBC
- Fingerprint: MD5
After you add an SFTP-SSH trigger or action to your workflow, you have to provide connection information for your SFTP server. When you provide your SSH private key for this connection, don't manually enter or edit the key, which might cause the connection to fail. Instead, make sure that you copy the key from your SSH private key file, and paste that key into the connection details. For more information, see the Connect to SFTP with SSH section later this article.
Basic knowledge about how to create logic apps
The logic app workflow where you want to access your SFTP account. To start with an SFTP-SSH trigger, create a blank logic app workflow. To use an SFTP-SSH action, start your workflow with another trigger, for example, the Recurrence trigger.
How SFTP-SSH triggers work
Polling behavior
SFTP-SSH triggers poll the SFTP file system and look for any file that changed since the last poll. Some tools let you preserve the timestamp when the files change. In these cases, you have to disable this feature so your trigger can work. Here are some common settings:
| SFTP client | Action |
|---|---|
| Winscp | Go to Options > Preferences > Transfer > Edit > Preserve timestamp > Disable |
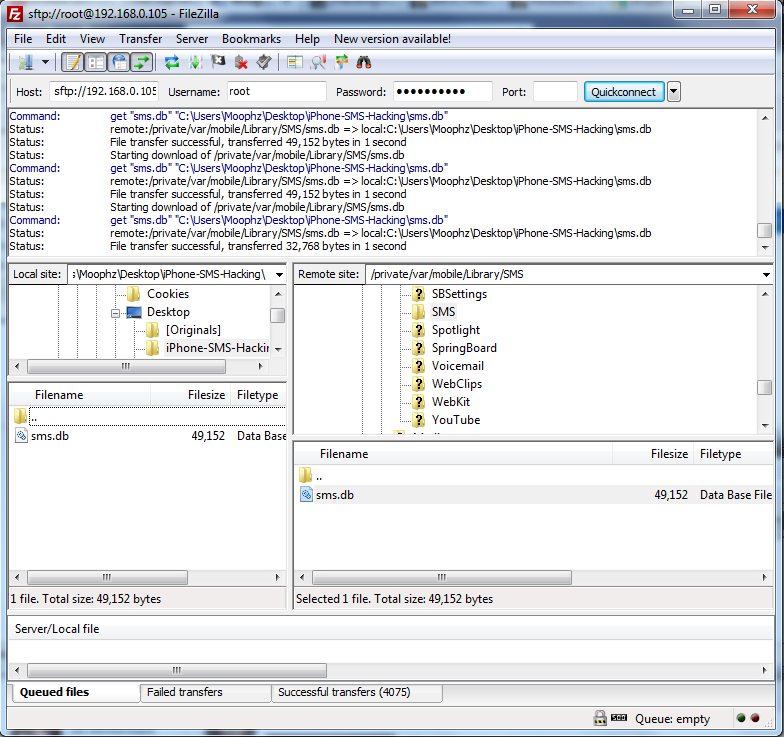
| FileZilla | Go to Transfer > Preserve timestamps of transferred files > Disable |
When a trigger finds a new file, the trigger checks that the new file is complete, and not partially written. For example, a file might have changes in progress when the trigger checks the file server. To avoid returning a partially written file, the trigger notes the timestamp for the file that has recent changes, but doesn't immediately return that file. The trigger returns the file only when polling the server again. Sometimes, this behavior might cause a delay that is up to twice the trigger's polling interval.
Trigger recurrence shift and drift
Connection-based triggers where you need to create a connection first, such as the SFTP-SSH trigger, differ from built-in triggers that run natively in Azure Logic Apps, such as the Recurrence trigger. In recurring connection-based triggers, the recurrence schedule isn't the only driver that controls execution, and the time zone only determines the initial start time. Subsequent runs depend on the recurrence schedule, the last trigger execution, and other factors that might cause run times to drift or produce unexpected behavior. For example, unexpected behavior can include failure to maintain the specified schedule when daylight saving time (DST) starts and ends. To make sure that the recurrence time doesn't shift when DST takes effect, manually adjust the recurrence. That way, your workflow continues to run at the expected time. Otherwise, the start time shifts one hour forward when DST starts and one hour backward when DST ends. For more information, see Recurrence for connection-based triggers.
Convert PuTTY-based key to OpenSSH
The PuTTY format and OpenSSH format use different file name extensions. The PuTTY format uses the .ppk, or PuTTY Private Key, file name extension. The OpenSSH format uses the .pem, or Privacy Enhanced Mail, file name extension. If your private key is in PuTTY format, and you have to use OpenSSH format, first convert the key to the OpenSSH format by following these steps:
Unix-based OS
If you don't have the PuTTY tools installed on your system, do that now, for example:
sudo apt-get install -y puttyRun this command, which creates a file that you can use with the SFTP-SSH connector:
puttygen <path-to-private-key-file-in-PuTTY-format> -O private-openssh -o <path-to-private-key-file-in-OpenSSH-format>For example:
puttygen /tmp/sftp/my-private-key-putty.ppk -O private-openssh -o /tmp/sftp/my-private-key-openssh.pem
Windows OS
If you haven't done so already, download the latest PuTTY Generator (puttygen.exe) tool, and then launch the tool.
On this screen, select Load.
Browse to your private key file in PuTTY format, and select Open.
From the Conversions menu, select Export OpenSSH key.
Save the private key file with the
.pemfile name extension.
Considerations
This section describes considerations to review when you use this connector's triggers and actions.
Use different SFTP folders for file upload and processing
On your SFTP server, use separate folders for storing uploaded files and for the trigger to monitor those files for processing. Otherwise, the trigger won't fire and behaves unpredictably, for example, skipping a random number of files that the trigger processes. However, this requirement means that you need a way to move files between those folders.
If this trigger problem happens, remove the files from the folder that the trigger monitors, and use a different folder to store the uploaded files.
Create file
To create a file on your SFTP server, you can use the SFTP-SSH Create file action. When this action creates the file, the Logic Apps service also automatically calls your SFTP server to get the file's metadata. However, if you move the newly created file before the Logic Apps service can make the call to get the metadata, you get a 404 error message, 'A reference was made to a file or folder which does not exist'. To skip reading the file's metadata after file creation, follow the steps to add and set the Get all file metadata property to No.
Connect to SFTP with SSH
When you add a trigger or action that connects to a service or system for the first time, the Logic App Designer prompts you to create a connection by providing the necessary information, which varies based on the connection, for example:
The name that you want to use for the new connection
The name for the system or server
Your user or account credentials
The authentication type to use
Sign in to the Azure portal, and open your logic app in Logic App Designer, if not open already.
For blank logic apps, in the search box, enter
sftp sshas your filter. Under the triggers list, select the trigger you want.-or-
For existing logic apps, under the last step where you want to add an action, select New step. In the search box, enter
sftp sshas your filter. Under the actions list, select the action you want.To add an action between steps, move your pointer over the arrow between steps. Select the plus sign (+) that appears, and then select Add an action.
Provide the necessary details for your connection.
Important
When you enter your SSH private key in the SSH private key property, follow these additional steps, which helpmake sure you provide the complete and correct value for this property. An invalid key causes the connection to fail.
Although you can use any text editor, here are sample steps that show how to correctly copy and paste your key by using Notepad.exe as an example.
Open your SSH private key file in a text editor. These steps use Notepad as the example.
On the Notepad Edit menu, select Select All.
Select Edit > Copy.
In the SFTP-SSH trigger or action, paste the complete copied key in the SSH private key property, which supports multiple lines. Don't manually enter or edit the key.
After you finish entering the connection details, select Create.
Now provide the necessary details for your selected trigger or action and continue building your logic app's workflow.
Override chunk size
To override the default adaptive behavior that chunking uses, you can specify a constant chunk size from 5 MB to 50 MB.
In the action's upper-right corner, select the ellipses button (..), and then select Settings.
Under Content Transfer, in the Chunk size property, enter an integer value from
5to50, for example:After you finish, select Done.
Examples
SFTP - SSH trigger: When a file is added or modified
This trigger starts a workflow when a file is added or changed on an SFTP server. As example follow-up actions, the workflow can use a condition to check whether the file content meets specified criteria. If the content meets the condition, the Get file content SFTP-SSH action can get the content, and then another SFTP-SSH action can put that file in a different folder on the SFTP server.
Enterprise example: You can use this trigger to monitor an SFTP folder for new files that represent customer orders. You can then use an SFTP-SSH action such as Get file content so you get the order's contents for further processing and store that order in an orders database.
SFTP - SSH action: Get file content using path
This action gets the content from a file on an SFTP server by specifying the file path. So for example, you can add the trigger from the previous example and a condition that the file's content must meet. If the condition is true, the action that gets the content can run.
Troubleshoot problems
Ssh Sftp Sshd_config
This section describes possible solutions to common errors or problems.
504 error: 'A connection attempt failed because the connected party did not properly respond after a period of time, or established connection failed because connected host has failed to respond' or 'Request to the SFTP server has taken more than '00:00:30' seconds'
This error can happen when your logic app can't successfully establish a connection with the SFTP server. There might be different reasons for this problem, so try these troubleshooting options:
The connection timeout is 20 seconds. Check that your SFTP server has good performance and intermediate devices, such as firewalls, aren't adding overhead.
If you have a firewall set up, make sure that you add the Managed connector IP addresses to the approved list. To find the IP addresses for your logic app's region, see Limits and configuration for Azure Logic Apps.
If this error happens intermittently, change the Retry policy setting on the SFTP-SSH action to a retry count higher than the default four retries.
Check whether SFTP server puts a limit on the number of connections from each IP address. If a limit exists, you might have to limit the number of concurrent logic app instances.
To reduce connection establishment cost, in the SSH configuration for your SFTP server, increase the ClientAliveInterval property to around one hour.
Review the SFTP server log to check whether the request from logic app reached the SFTP server. To get more information about the connectivity problem, you can also run a network trace on your firewall and your SFTP server.
404 error: 'A reference was made to a file or folder which does not exist'
This error can happen when your workflow creates a file on your SFTP server with the SFTP-SSH Create file action, but immediately moves that file before the Logic Apps service can get the file's metadata. After effects playback. When your workflow runs the Create file action, the Logic Apps service automatically calls your SFTP server to get the file's metadata. However, if your logic app moves the file, the Logic Apps service can no longer find the file so you get the 404 error message.
If you can't avoid or delay moving the file, you can skip reading the file's metadata after file creation instead by following these steps:
Windows Sftp Ssh_config
In the Create file action, open the Add new parameter list, select the Get all file metadata property, and set the value to No.
If you need this file metadata later, you can use the Get file metadata action.
Connector reference
For more technical details about this connector, such as triggers, actions, and limits as described by the connector's Swagger file, see the connector's reference page.
Note
For logic apps in an integration service environment (ISE),this connector's ISE-labeled version require chunking to use the ISE message limits instead.
Next steps
- Learn about other Logic Apps connectors
This section of Getting Started assumes that:
- You have recently installed Bitvise SSH Server.
- You have installed Bitvise SSH Client on the same computer as the server to aid with initial setup.
- You have learned about how the SSH Server is used with Windows accounts and virtual accounts.
- You would like to configure the SSH Server to provide file transfer access via SFTP and SCP.
The SSH Server supports file transfer protocols SFTP and SCP. Both of these run over SSH.
The SSH Server does not currently support plain FTP, or FTPS (FTP over TLS/SSL).
We plan to support FTPS in a future version.
First, open Easy SSH Server settings and create a virtual account:
For virtual accounts, default settings are already to:
- Allow file transfer.
- Do not allow shell access (or exec requests).
- Do not allow port forwarding.
The main settings to configure are the virtual account name, password, and the root directory for file transfers.
It is important that accounts which should have limited access to the server's filesystem are not granted a shell access type that provides Command Prompt, PowerShell, bash, or similar open-ended terminal shell access.
When a user is given open-ended terminal shell access, this shell is a third-party application that does not know about the SSH Server's virtual filesystem, and does not respect settings such as Limit to root directory.
Users who are configured with Shell access type set to No shell access will not be able to connect using a terminal SSH client, such as PuTTY. However, they will be able to connect with a file transfer client, or if the terminal client is instructed to not try opening a terminal shell.
This example uses a virtual account with the default security context. The default security context is a Windows account named BvSsh_VirtualUsers which is created by the SSH Server. This account is not created until you:
- Create at last one virtual account.
- Start the SSH Server with at least one virtual account created.
Therefore, to make sure the BvSsh_VirtualUsers account exists, start the SSH Server and stop it.
If you experience issues finding the BvSsh_VirtualUsers account, check Q440 and Q460 in the SSH Server Usage FAQ.
We will show a setup using virtual accounts, where the SSH client is not intended to have access to the server's entire filesystem. For this purpose, we need a directory which the SFTP or SCP client will be able to access. We will use Windows File Explorer to create the directory C:SftpRoot:
This example uses a virtual account with the default security context. We therefore need to ensure that the Windows account BvSsh_VirtualUsers can access files and subdirectories of the SFTP root directory we have created:
The Windows account BvSsh_VirtualUsers is a member of the Users group, but this group does not have Windows filesystem permissions to write to C:SftpRoot. We will need to add permissions to allow virtual accounts to upload.
Still using Windows File Explorer, we will use Advanced Security Settings to grant Windows filesystem permissions to the contents of C:SftpRoot to the BvSsh_VirtualUsers account:
We have identified the account for which we want to add permissions. We configure them as follows:This will allow virtual accounts to have full control over the files and subfolders in the C:SftpRoot directory; but not over the parent directory itself.
It is possible to use this interface to grant more nuanced permissions also.
To control users' access to files and directories, you may use any combination of Windows filesystem permissions; mount point permissions configured in Advanced SSH Server settings; or both.
We will now use the SSH Client, which we have previously installed on the same computer, to verify the operation of our virtual account:
We use the same localhost SSH Client profile we created previously. We enter the new username and password and press Login. In this case, we have used the Options tab to disable automatic opening of the SFTP and terminal windows. Therefore, we click New SFTP window when the SSH Client connects.
If everything has gone well so far, the SFTP window opens.
We have used Notepad to create a test file on the desktop, named 'Test File.txt'. We will upload this file to the server:
If we have configured Windows filesystem permissions correctly, the upload succeeds:
We have established that SFTP works. Sketch of gown designs. Now, make sure that the user cannot access the terminal shell:
We can also try to configure a server-to-client (S2C) port forwarding rule, to verify that the server does not permit it:
To perform the same check for client-to-server port forwarding (C2S), it is necessary not only to configure the rule, but also to try to connect.
